搜索到
381
篇与
moonjerx
的结果
-
 Docker容器保存为新镜像 一、Docker容器的保存在使用Docker的过程中,我们常常需要在容器中创建文件或者修改配置文件等操作。如果不保存容器,那么当容器停止之后,我们就会失去这些操作的痕迹,下次再次启动容器时,还需要重新操作一遍。为了避免这种情况的发生,我们可以将在容器中的操作保存下来,使得下次启动容器时,可以直接继续上次的操作。Docker提供了几种方式来保存容器,包括利用 commit 命令保存容器变更,以及利用 Dockerfile 进行构建。其中,利用 commit 命令保存容器变更是比较常用的方式之一。二、利用 commit 命令保存容器变更commit 命令可以将容器的改动保存为一个新的镜像。其命令格式为:docker commit [OPTIONS] CONTAINER [REPOSITORY[:TAG]]其中,OPTIONS 可以省略,CONTAINER 为需保存的容器 ID 或者容器的名称,REPOSITORY 为保存时的镜像名称,TAG 为镜像的标签。以下是一个示例,其中将容器的改动保存为新镜像:docker run -it --name container1 ubuntu:18.04 // 在容器中安装vim编辑器 apt update apt install vim docker commit container1 myubuntu:v1这样,容器中安装的vim编辑器便被保存为了一个新的镜像 myubuntu:v1。三、利用 Dockerfile 进行构建Dockerfile 是一种用来描述镜像构建过程的文件。通过编写 Dockerfile 文件,我们可以很方便地构建出自己的镜像。具体过程如下:编写 Dockerfile构建镜像创建容器下面是一个简单的示例,利用 Dockerfile 构建含有 Nginx 服务器的镜像:FROM ubuntu:18.04 RUN apt-get update && apt-get install -y nginx CMD ["nginx", "-g", "daemon off;"] EXPOSE 80这段脚本在 Ubuntu 镜像的基础上安装了 Nginx,并指定了启动时运行的命令。接下来,构建镜像:docker build -t mynginx:v1这样,我们就可以使用这个镜像来创建容器:docker run -d -p 80:80 mynginx:v1其中,-d 指定使用守护进程方式运行容器,-p 80:80 表示将容器中的 80 端口映射到主机的 80 端口。四、Docker容器保存为新镜像的优点方便还原:利用 Docker 容器保存为新镜像,我们可以很方便地还原到上次操作的状态。容器复用:保存为新镜像后,我们可以将其上传到 Docker Hub 等镜像仓库,并在不同的机器或环境中复用该镜像。降低容器构建成本:Docker 构建新镜像时,可以利用已有的镜像作为基础镜像,这样可以有效降低容器构建成本。五、总结本文对利用 Docker 容器保存为新镜像这一重要主题进行了详细的阐述。我们从 Docker 容器的保存、利用 commit 命令保存容器变更、利用 Dockerfile 进行构建、Docker容器保存为新镜像的优点等多个方面进行了分析。在实际应用中,我们可以根据具体需要进行选择,达到最佳效果。
Docker容器保存为新镜像 一、Docker容器的保存在使用Docker的过程中,我们常常需要在容器中创建文件或者修改配置文件等操作。如果不保存容器,那么当容器停止之后,我们就会失去这些操作的痕迹,下次再次启动容器时,还需要重新操作一遍。为了避免这种情况的发生,我们可以将在容器中的操作保存下来,使得下次启动容器时,可以直接继续上次的操作。Docker提供了几种方式来保存容器,包括利用 commit 命令保存容器变更,以及利用 Dockerfile 进行构建。其中,利用 commit 命令保存容器变更是比较常用的方式之一。二、利用 commit 命令保存容器变更commit 命令可以将容器的改动保存为一个新的镜像。其命令格式为:docker commit [OPTIONS] CONTAINER [REPOSITORY[:TAG]]其中,OPTIONS 可以省略,CONTAINER 为需保存的容器 ID 或者容器的名称,REPOSITORY 为保存时的镜像名称,TAG 为镜像的标签。以下是一个示例,其中将容器的改动保存为新镜像:docker run -it --name container1 ubuntu:18.04 // 在容器中安装vim编辑器 apt update apt install vim docker commit container1 myubuntu:v1这样,容器中安装的vim编辑器便被保存为了一个新的镜像 myubuntu:v1。三、利用 Dockerfile 进行构建Dockerfile 是一种用来描述镜像构建过程的文件。通过编写 Dockerfile 文件,我们可以很方便地构建出自己的镜像。具体过程如下:编写 Dockerfile构建镜像创建容器下面是一个简单的示例,利用 Dockerfile 构建含有 Nginx 服务器的镜像:FROM ubuntu:18.04 RUN apt-get update && apt-get install -y nginx CMD ["nginx", "-g", "daemon off;"] EXPOSE 80这段脚本在 Ubuntu 镜像的基础上安装了 Nginx,并指定了启动时运行的命令。接下来,构建镜像:docker build -t mynginx:v1这样,我们就可以使用这个镜像来创建容器:docker run -d -p 80:80 mynginx:v1其中,-d 指定使用守护进程方式运行容器,-p 80:80 表示将容器中的 80 端口映射到主机的 80 端口。四、Docker容器保存为新镜像的优点方便还原:利用 Docker 容器保存为新镜像,我们可以很方便地还原到上次操作的状态。容器复用:保存为新镜像后,我们可以将其上传到 Docker Hub 等镜像仓库,并在不同的机器或环境中复用该镜像。降低容器构建成本:Docker 构建新镜像时,可以利用已有的镜像作为基础镜像,这样可以有效降低容器构建成本。五、总结本文对利用 Docker 容器保存为新镜像这一重要主题进行了详细的阐述。我们从 Docker 容器的保存、利用 commit 命令保存容器变更、利用 Dockerfile 进行构建、Docker容器保存为新镜像的优点等多个方面进行了分析。在实际应用中,我们可以根据具体需要进行选择,达到最佳效果。 -
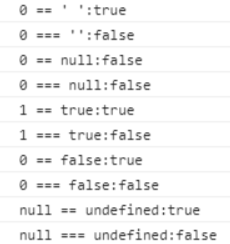
 Javascript中0 == ""的判断结果为true $(function() { console.log("0 == ' ':" + (0 == '')); console.log("0 === '':" + (0 === '')); console.log("0 == null:" + (0 == null)); console.log("0 === null:" + (0 === null)); console.log("1 == true:" + (1 == true)); console.log("1 === true:" + (1 === true)); console.log("0 == false:" + (0 == false)); console.log("0 === false:" + (0 === false)); console.log("null == undefined:" + (null == undefined)); console.log("null === undefined:" + (null === undefined)); })先来说一下 === 吧1、首先是判断两值的类型是否一样,不一样就不相等。2、字符串为例,需要两个字符串的长度一致和每个字符的位置都一致才相等。3、如果两都是引用,比较引用是否一致。4、从上面的运行结果可以看出 null === undefined 是 false的,因为两个值的类型不一样。其实,js的 === 有点类似 Java 里面的 equals 方法。最后就是 js 的 == 了1、如果两值的类型一样,然后就进行 === 比较。2、如果两值的类型不一样,就先转为相同的类型再进行比较。【1】从上面的运行结果可以看到 null == undefined 为 true 的,null == undefined 比较时是不进行转换的,并且规定 null 等于 undefined。【2】如果不同类型与 true 或者 false 进行比较时,会先把true转成 1 ,false 转成 0 ,再进行比较。这就解释了为什么 0 == false 和 1== true 为 true 了。【3】如果一个是基本数据类型一个是对象,那会先把对象先转成基本数据类型,再进行比较。【4】本文的重点:0 == ' ' 为 true,因为0可以为 false,空格或空值也为 false,所以它们相等。我们 if 判断 if(null) 是false,那么为什么 0 == null 是 false呢,是因为null 和 undefined 和 NaN 是特殊值,不进行转换的。NaN == null ,NaN == undefined 都为 false,无论 NaN == 啥都为 false。
Javascript中0 == ""的判断结果为true $(function() { console.log("0 == ' ':" + (0 == '')); console.log("0 === '':" + (0 === '')); console.log("0 == null:" + (0 == null)); console.log("0 === null:" + (0 === null)); console.log("1 == true:" + (1 == true)); console.log("1 === true:" + (1 === true)); console.log("0 == false:" + (0 == false)); console.log("0 === false:" + (0 === false)); console.log("null == undefined:" + (null == undefined)); console.log("null === undefined:" + (null === undefined)); })先来说一下 === 吧1、首先是判断两值的类型是否一样,不一样就不相等。2、字符串为例,需要两个字符串的长度一致和每个字符的位置都一致才相等。3、如果两都是引用,比较引用是否一致。4、从上面的运行结果可以看出 null === undefined 是 false的,因为两个值的类型不一样。其实,js的 === 有点类似 Java 里面的 equals 方法。最后就是 js 的 == 了1、如果两值的类型一样,然后就进行 === 比较。2、如果两值的类型不一样,就先转为相同的类型再进行比较。【1】从上面的运行结果可以看到 null == undefined 为 true 的,null == undefined 比较时是不进行转换的,并且规定 null 等于 undefined。【2】如果不同类型与 true 或者 false 进行比较时,会先把true转成 1 ,false 转成 0 ,再进行比较。这就解释了为什么 0 == false 和 1== true 为 true 了。【3】如果一个是基本数据类型一个是对象,那会先把对象先转成基本数据类型,再进行比较。【4】本文的重点:0 == ' ' 为 true,因为0可以为 false,空格或空值也为 false,所以它们相等。我们 if 判断 if(null) 是false,那么为什么 0 == null 是 false呢,是因为null 和 undefined 和 NaN 是特殊值,不进行转换的。NaN == null ,NaN == undefined 都为 false,无论 NaN == 啥都为 false。 -
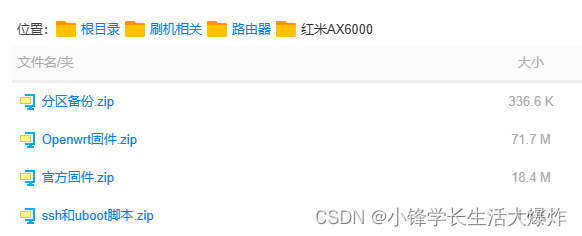
 红米ax6000刷openwrt 原文链接 相关文件已为大家上传到国内云盘:https://xfxuezhang.lanzouo.com/b09uh21kf密码:axqt开启SSH1、下载官方指定版本固件:https://share.qust.me/redmi-ax6000-1.2.8.bin2、进入路由器后台升级固件:http://192.168.31.1/cgi-bin/luci/web3、获取路由器 stock4、开启调试模式,替换 {STOK}http://192.168.31.1/cgi-bin/luci/;stok={token}/api/misystem/set_sys_time?timezone=%20%27%20%3B%20zz%3D%24%28dd%20if%3D%2Fdev%2Fzero%20bs%3D1%20count%3D2%202%3E%2Fdev%2Fnull%29%20%3B%20printf%20%27%A5%5A%25c%25c%27%20%24zz%20%24zz%20%7C%20mtd%20write%20-%20crash%20%3B%20返回:{"code":0}5、请求重启,替换 {STOK}http://192.168.31.1/cgi-bin/luci/;stok={token}/api/misystem/set_sys_time?timezone=%20%27%20%3b%20reboot%20%3b%20返回:{"code":0}。等待重启完成(白灯亮起),并重新登录。6、设置 Bdata 永久开启 telnet,替换 {STOK}http://192.168.31.1/cgi-bin/luci/;stok={token}/api/misystem/set_sys_time?timezone=%20%27%20%3B%20bdata%20set%20telnet_en%3D1%20%3B%20bdata%20set%20ssh_en%3D1%20%3B%20bdata%20set%20uart_en%3D1%20%3B%20bdata%20commit%20%3B%20返回:{"code":0}。7、请求重启,替换 {STOK}http://192.168.31.1/cgi-bin/luci/;stok={token}/api/misystem/set_sys_time?timezone=%20%27%20%3b%20reboot%20%3b%20返回:{"code":0}。等待重启完成(白灯亮起),并重新登录。8、telnet 连接开启 sshtelnet 192.168.31.1没有密码。9、解锁SSHcd /tmp && curl --silent -O https://fastly.jsdelivr.net/gh/miaoermua/unlock-redmi-ax6000@main/setup.sh && chmod +x setup.sh && ./setup.sh以上sh步骤包括:设置 ssh 密码为 admin、并永久开启 SSH、并从开发模式修改回正常的模式,并重启。刷入UBoot1、ssh登录路由器,密码为adminssh root@192.168.31.12、下载ubootcd /tmp && curl --silent -O https://fastly.jsdelivr.net/gh/miaoermua/unlock-redmi-ax6000@main/uboot.sh && chmod +x uboot.sh && ./uboot.sh以上sh步骤包括:备份一下原本的引导分区、进行下载 U-Boot3、从路由器下载分区文件,没有他你就不能恢复到小米原厂系统!可以使用 WinSCP 连接小米路由器,协议选择 scp 主机填 192.168.31.1,账号 root 密码 admin。或者直接新开一个窗口,执行:scp root@192.168.31.1:/tmp/mtd4_Factory.bin E:\ scp root@192.168.31.1:/tmp/mtd5_FIP.bin E:\4、刷入ubootmtd erase FIP mtd write /tmp/mt7986_redmi_ax6000-fip-fixed-parts.bin FIP mtd verify /tmp/mt7986_redmi_ax6000-fip-fixed-parts.bin FIP刷入Openwrt1、设置电脑静态地址{callout color="#f0ad4e"}Tip: 在接下来的步骤网口 1 将作为 Wan 口,网口 234 为 Lan;不支持自适应!请将连接电脑的网线插入到 234 任意 Lan 网口里。{/callout}点击左下角 Windows 微标在键盘上输入 控制面板 回车,打开 控制面板 - 查看网络状态和任务 选择到 以太网 - 属性-Internet 协议版本 4 (TCP/IPv4)-属性选择使用下面的 IP 地址,依次填入IP 地址:192.168.31.2子网掩码:255.255.255.0网关地址:192.168.31.1点下 确定 即可2、上传固件接下来拔掉红米 AX6000 的电源,将牙签戳入路由器的 reset 口上同时接入电源,按住心里默念 15 秒然后松开 reset。就进入到大神编译好的 U-Boot 程序了。{callout color="#f0ad4e"}此时 U-Boot 不会亮 LED 灯,可以观察电脑的网口是否闪烁以检查路由器是否运行,reset 可以多按几秒不能少于 15 秒!{/callout} 这里点击选择文件找到下载编译好的 CatWrt For RedmiAX6000 的固件。 Github:Release CatWrt-v23.2 mt7986a · miaoermua/CatWrt · GitHub 然后点击 Update,固件将会上传到 U-Boot 里点击刷入,就会检查你的包是否兼容。第一次如果这里就提示 Update Failed 报错的,这里很正常,返回再次上传固件。这次就很轻松就刷入固件了,刷入当出现 Upgrade complete! 并且伴随 LED 白灯亮起 U-Boot 这块就完成了。(就算一直在转圈圈,但路由器亮起了白灯,那也算成功了。)注意电脑需要再控制中心将静态地址恢复为“自动获取”。设置Openwrt{callout color="#f0ad4e"}注意电脑需要再控制中心将静态地址恢复为“自动获取”。{/callout}默认地址是 192.168.1.4这里还得将我们之前设置的静态地址改为 DHCP 自动获取在浏览器中登录路由器后台 192.168.1.4账号 root 密码 password即可进入 CatWrt首先需要设置 Lan 口配置,点击 网络 - 接口-Lan-编辑地址我们这里不修改,挺好的网关这里设置本机地址 192.168.1.4广播这里设置 192.168.1.0DNS 我这里就设置阿里和腾讯的公共 DNS 地址IPv6 是默认打开,DHCP 这里默认 50 起也不是不行我这里我喜欢改到 20,因人而异吧IPv6 这里的 DNS 我们设置在 240C::6666保存并应用,如果你修改了本机的地址这里路由器可能无限转圈圈,就需要重启一下重新在地址栏里输入你的地址即可接下来接着设置 Wan 口,点击 网络 - 接口-Wan-编辑刷回小米原厂固件{callout color="#f0ad4e"}参考: 恢复分区 如果你使用 U-Boot 刷入了其他固件可能不包含 kmod-mtd-rm 即不能解锁分区并还原。{/callout}1、使用 WinSCP 连接上红米 AX60001、使用 WinSCP 连接上红米 AX60002、恢复分区将之前下载的备份好的 mtd5_FIP.bin 分区文件上传到 /tmp 目录里后,执行命令解锁 FIP 分区,即可恢复官方 U-Boot 分区{callout color="#f0ad4e"}insmod mtd-rw.ko i_want_a_brick=1md5sum /tmp/mtd5_FIP.binmtd write /tmp/mtd5_FIP.bin FIPmtd verify /tmp/mtd5_FIP.bin FIP{/callout}后面就可以断电用小米官方修复工具来修复了3、使用小米官方修复工具。 小米修复工具这里比较多注意事项,首先关掉Windows Defender 防火墙和杀软,有多个网卡的记得得把多余的网卡禁用掉,拔掉 Wan 口网线(网口 1)和电源线。 在小米官方修复工具中把我们预先下好的官方固件选上,下一步网卡这里我这里只有一个继续,接着一手牙签戳进 reset 孔,一手插电,长按直到蓝色 LED 灯长亮转为了橙灯闪烁后松开 reset。等待一会就会出现刷入弹窗,等进度跑完,路由器的蓝色的 LED 灯闪烁提示你拔掉电源重启,我们拔掉电源重新插上等待一会,我们就恢复了原厂固件
红米ax6000刷openwrt 原文链接 相关文件已为大家上传到国内云盘:https://xfxuezhang.lanzouo.com/b09uh21kf密码:axqt开启SSH1、下载官方指定版本固件:https://share.qust.me/redmi-ax6000-1.2.8.bin2、进入路由器后台升级固件:http://192.168.31.1/cgi-bin/luci/web3、获取路由器 stock4、开启调试模式,替换 {STOK}http://192.168.31.1/cgi-bin/luci/;stok={token}/api/misystem/set_sys_time?timezone=%20%27%20%3B%20zz%3D%24%28dd%20if%3D%2Fdev%2Fzero%20bs%3D1%20count%3D2%202%3E%2Fdev%2Fnull%29%20%3B%20printf%20%27%A5%5A%25c%25c%27%20%24zz%20%24zz%20%7C%20mtd%20write%20-%20crash%20%3B%20返回:{"code":0}5、请求重启,替换 {STOK}http://192.168.31.1/cgi-bin/luci/;stok={token}/api/misystem/set_sys_time?timezone=%20%27%20%3b%20reboot%20%3b%20返回:{"code":0}。等待重启完成(白灯亮起),并重新登录。6、设置 Bdata 永久开启 telnet,替换 {STOK}http://192.168.31.1/cgi-bin/luci/;stok={token}/api/misystem/set_sys_time?timezone=%20%27%20%3B%20bdata%20set%20telnet_en%3D1%20%3B%20bdata%20set%20ssh_en%3D1%20%3B%20bdata%20set%20uart_en%3D1%20%3B%20bdata%20commit%20%3B%20返回:{"code":0}。7、请求重启,替换 {STOK}http://192.168.31.1/cgi-bin/luci/;stok={token}/api/misystem/set_sys_time?timezone=%20%27%20%3b%20reboot%20%3b%20返回:{"code":0}。等待重启完成(白灯亮起),并重新登录。8、telnet 连接开启 sshtelnet 192.168.31.1没有密码。9、解锁SSHcd /tmp && curl --silent -O https://fastly.jsdelivr.net/gh/miaoermua/unlock-redmi-ax6000@main/setup.sh && chmod +x setup.sh && ./setup.sh以上sh步骤包括:设置 ssh 密码为 admin、并永久开启 SSH、并从开发模式修改回正常的模式,并重启。刷入UBoot1、ssh登录路由器,密码为adminssh root@192.168.31.12、下载ubootcd /tmp && curl --silent -O https://fastly.jsdelivr.net/gh/miaoermua/unlock-redmi-ax6000@main/uboot.sh && chmod +x uboot.sh && ./uboot.sh以上sh步骤包括:备份一下原本的引导分区、进行下载 U-Boot3、从路由器下载分区文件,没有他你就不能恢复到小米原厂系统!可以使用 WinSCP 连接小米路由器,协议选择 scp 主机填 192.168.31.1,账号 root 密码 admin。或者直接新开一个窗口,执行:scp root@192.168.31.1:/tmp/mtd4_Factory.bin E:\ scp root@192.168.31.1:/tmp/mtd5_FIP.bin E:\4、刷入ubootmtd erase FIP mtd write /tmp/mt7986_redmi_ax6000-fip-fixed-parts.bin FIP mtd verify /tmp/mt7986_redmi_ax6000-fip-fixed-parts.bin FIP刷入Openwrt1、设置电脑静态地址{callout color="#f0ad4e"}Tip: 在接下来的步骤网口 1 将作为 Wan 口,网口 234 为 Lan;不支持自适应!请将连接电脑的网线插入到 234 任意 Lan 网口里。{/callout}点击左下角 Windows 微标在键盘上输入 控制面板 回车,打开 控制面板 - 查看网络状态和任务 选择到 以太网 - 属性-Internet 协议版本 4 (TCP/IPv4)-属性选择使用下面的 IP 地址,依次填入IP 地址:192.168.31.2子网掩码:255.255.255.0网关地址:192.168.31.1点下 确定 即可2、上传固件接下来拔掉红米 AX6000 的电源,将牙签戳入路由器的 reset 口上同时接入电源,按住心里默念 15 秒然后松开 reset。就进入到大神编译好的 U-Boot 程序了。{callout color="#f0ad4e"}此时 U-Boot 不会亮 LED 灯,可以观察电脑的网口是否闪烁以检查路由器是否运行,reset 可以多按几秒不能少于 15 秒!{/callout} 这里点击选择文件找到下载编译好的 CatWrt For RedmiAX6000 的固件。 Github:Release CatWrt-v23.2 mt7986a · miaoermua/CatWrt · GitHub 然后点击 Update,固件将会上传到 U-Boot 里点击刷入,就会检查你的包是否兼容。第一次如果这里就提示 Update Failed 报错的,这里很正常,返回再次上传固件。这次就很轻松就刷入固件了,刷入当出现 Upgrade complete! 并且伴随 LED 白灯亮起 U-Boot 这块就完成了。(就算一直在转圈圈,但路由器亮起了白灯,那也算成功了。)注意电脑需要再控制中心将静态地址恢复为“自动获取”。设置Openwrt{callout color="#f0ad4e"}注意电脑需要再控制中心将静态地址恢复为“自动获取”。{/callout}默认地址是 192.168.1.4这里还得将我们之前设置的静态地址改为 DHCP 自动获取在浏览器中登录路由器后台 192.168.1.4账号 root 密码 password即可进入 CatWrt首先需要设置 Lan 口配置,点击 网络 - 接口-Lan-编辑地址我们这里不修改,挺好的网关这里设置本机地址 192.168.1.4广播这里设置 192.168.1.0DNS 我这里就设置阿里和腾讯的公共 DNS 地址IPv6 是默认打开,DHCP 这里默认 50 起也不是不行我这里我喜欢改到 20,因人而异吧IPv6 这里的 DNS 我们设置在 240C::6666保存并应用,如果你修改了本机的地址这里路由器可能无限转圈圈,就需要重启一下重新在地址栏里输入你的地址即可接下来接着设置 Wan 口,点击 网络 - 接口-Wan-编辑刷回小米原厂固件{callout color="#f0ad4e"}参考: 恢复分区 如果你使用 U-Boot 刷入了其他固件可能不包含 kmod-mtd-rm 即不能解锁分区并还原。{/callout}1、使用 WinSCP 连接上红米 AX60001、使用 WinSCP 连接上红米 AX60002、恢复分区将之前下载的备份好的 mtd5_FIP.bin 分区文件上传到 /tmp 目录里后,执行命令解锁 FIP 分区,即可恢复官方 U-Boot 分区{callout color="#f0ad4e"}insmod mtd-rw.ko i_want_a_brick=1md5sum /tmp/mtd5_FIP.binmtd write /tmp/mtd5_FIP.bin FIPmtd verify /tmp/mtd5_FIP.bin FIP{/callout}后面就可以断电用小米官方修复工具来修复了3、使用小米官方修复工具。 小米修复工具这里比较多注意事项,首先关掉Windows Defender 防火墙和杀软,有多个网卡的记得得把多余的网卡禁用掉,拔掉 Wan 口网线(网口 1)和电源线。 在小米官方修复工具中把我们预先下好的官方固件选上,下一步网卡这里我这里只有一个继续,接着一手牙签戳进 reset 孔,一手插电,长按直到蓝色 LED 灯长亮转为了橙灯闪烁后松开 reset。等待一会就会出现刷入弹窗,等进度跑完,路由器的蓝色的 LED 灯闪烁提示你拔掉电源重启,我们拔掉电源重新插上等待一会,我们就恢复了原厂固件 -
 openwrt软件源opkg 安装openvpnopkg update opkg install openvpn-easy-rsa openvpn-mbedtls luci-app-openvpn清华源src/gz openwrt_core https://mirrors.tuna.tsinghua.edu.cn/openwrt/releases/22.03.3/targets/ramips/mt7621/packages src/gz openwrt_base https://mirrors.tuna.tsinghua.edu.cn/openwrt/releases/22.03.3/packages/mipsel_24kc/base src/gz openwrt_luci https://mirrors.tuna.tsinghua.edu.cn/openwrt/releases/22.03.3/packages/mipsel_24kc/luci src/gz openwrt_packages https://mirrors.tuna.tsinghua.edu.cn/openwrt/releases/22.03.3/packages/mipsel_24kc/packages src/gz openwrt_routing https://mirrors.tuna.tsinghua.edu.cn/openwrt/releases/22.03.3/packages/mipsel_24kc/routing src/gz openwrt_telephony https://mirrors.tuna.tsinghua.edu.cn/openwrt/releases/22.03.3/packages/mipsel_24kc/telephony腾讯源src/gz openwrt_core https://mirrors.cloud.tencent.com/lede/snapshots/targets/ipq40xx/generic/packages src/gz openwrt_base https://mirrors.cloud.tencent.com/lede/snapshots/packages/arm_cortex-a7_neon-vfpv4/base src/gz openwrt_helloworld https://mirrors.cloud.tencent.com/lede/snapshots/packages/arm_cortex-a7_neon-vfpv4/helloworld src/gz openwrt_luci https://mirrors.cloud.tencent.com/lede/releases/18.06.9/packages/arm_cortex-a7_neon-vfpv4/luci src/gz openwrt_packages https://mirrors.cloud.tencent.com/lede/snapshots/packages/arm_cortex-a7_neon-vfpv4/packages src/gz openwrt_routing https://mirrors.cloud.tencent.com/lede/snapshots/packages/arm_cortex-a7_neon-vfpv4/routing src/gz openwrt_telephony https://mirrors.cloud.tencent.com/lede/snapshots/packages/arm_cortex-a7_neon-vfpv4/telephony 阿里云https://mirrors.aliyun.com/openwrt/releases/18.06.8/targets/brcm2708/bcm2710/packages/ https://mirrors.aliyun.com/openwrt/releases/18.06.8/packages/aarch64_cortex-a53/base/ https://mirrors.aliyun.com/openwrt/releases/18.06.8/packages/aarch64_cortex-a53/luci/ https://mirrors.aliyun.com/openwrt/releases/18.06.8/packages/aarch64_cortex-a53/packages/ https://mirrors.aliyun.com/openwrt/releases/18.06.8/packages/aarch64_cortex-a53/routing/其他src/gz openwrt_base https://openwrt.888913.gq/x86_64/base src/gz openwrt_luci https://openwrt.888913.gq/x86_64/luci src/gz openwrt_packages https://openwrt.888913.gq/x86_64/packages src/gz openwrt_routing https://openwrt.888913.gq/x86_64/routing src/gz openwrt_telephony https://openwrt.888913.gq/x86_64/telephonyhttps://downloads.openwrt.org/releases/22.03.2/targets/ath79/generic/packages/Packages.gz https://downloads.openwrt.org/releases/22.03.2/packages/mips_24kc/base/Packages.gz https://downloads.openwrt.org/releases/22.03.2/packages/mips_24kc/luci/Packages.gz https://downloads.openwrt.org/releases/22.03.2/packages/mips_24kc/packages/Packages.gz https://downloads.openwrt.org/releases/22.03.2/packages/mips_24kc/routing/Packages.gz https://downloads.openwrt.org/releases/22.03.2/packages/mips_24kc/telephony/Packages.gz
openwrt软件源opkg 安装openvpnopkg update opkg install openvpn-easy-rsa openvpn-mbedtls luci-app-openvpn清华源src/gz openwrt_core https://mirrors.tuna.tsinghua.edu.cn/openwrt/releases/22.03.3/targets/ramips/mt7621/packages src/gz openwrt_base https://mirrors.tuna.tsinghua.edu.cn/openwrt/releases/22.03.3/packages/mipsel_24kc/base src/gz openwrt_luci https://mirrors.tuna.tsinghua.edu.cn/openwrt/releases/22.03.3/packages/mipsel_24kc/luci src/gz openwrt_packages https://mirrors.tuna.tsinghua.edu.cn/openwrt/releases/22.03.3/packages/mipsel_24kc/packages src/gz openwrt_routing https://mirrors.tuna.tsinghua.edu.cn/openwrt/releases/22.03.3/packages/mipsel_24kc/routing src/gz openwrt_telephony https://mirrors.tuna.tsinghua.edu.cn/openwrt/releases/22.03.3/packages/mipsel_24kc/telephony腾讯源src/gz openwrt_core https://mirrors.cloud.tencent.com/lede/snapshots/targets/ipq40xx/generic/packages src/gz openwrt_base https://mirrors.cloud.tencent.com/lede/snapshots/packages/arm_cortex-a7_neon-vfpv4/base src/gz openwrt_helloworld https://mirrors.cloud.tencent.com/lede/snapshots/packages/arm_cortex-a7_neon-vfpv4/helloworld src/gz openwrt_luci https://mirrors.cloud.tencent.com/lede/releases/18.06.9/packages/arm_cortex-a7_neon-vfpv4/luci src/gz openwrt_packages https://mirrors.cloud.tencent.com/lede/snapshots/packages/arm_cortex-a7_neon-vfpv4/packages src/gz openwrt_routing https://mirrors.cloud.tencent.com/lede/snapshots/packages/arm_cortex-a7_neon-vfpv4/routing src/gz openwrt_telephony https://mirrors.cloud.tencent.com/lede/snapshots/packages/arm_cortex-a7_neon-vfpv4/telephony 阿里云https://mirrors.aliyun.com/openwrt/releases/18.06.8/targets/brcm2708/bcm2710/packages/ https://mirrors.aliyun.com/openwrt/releases/18.06.8/packages/aarch64_cortex-a53/base/ https://mirrors.aliyun.com/openwrt/releases/18.06.8/packages/aarch64_cortex-a53/luci/ https://mirrors.aliyun.com/openwrt/releases/18.06.8/packages/aarch64_cortex-a53/packages/ https://mirrors.aliyun.com/openwrt/releases/18.06.8/packages/aarch64_cortex-a53/routing/其他src/gz openwrt_base https://openwrt.888913.gq/x86_64/base src/gz openwrt_luci https://openwrt.888913.gq/x86_64/luci src/gz openwrt_packages https://openwrt.888913.gq/x86_64/packages src/gz openwrt_routing https://openwrt.888913.gq/x86_64/routing src/gz openwrt_telephony https://openwrt.888913.gq/x86_64/telephonyhttps://downloads.openwrt.org/releases/22.03.2/targets/ath79/generic/packages/Packages.gz https://downloads.openwrt.org/releases/22.03.2/packages/mips_24kc/base/Packages.gz https://downloads.openwrt.org/releases/22.03.2/packages/mips_24kc/luci/Packages.gz https://downloads.openwrt.org/releases/22.03.2/packages/mips_24kc/packages/Packages.gz https://downloads.openwrt.org/releases/22.03.2/packages/mips_24kc/routing/Packages.gz https://downloads.openwrt.org/releases/22.03.2/packages/mips_24kc/telephony/Packages.gz -

您的IP: